A Visual Introduction to Machine Learning
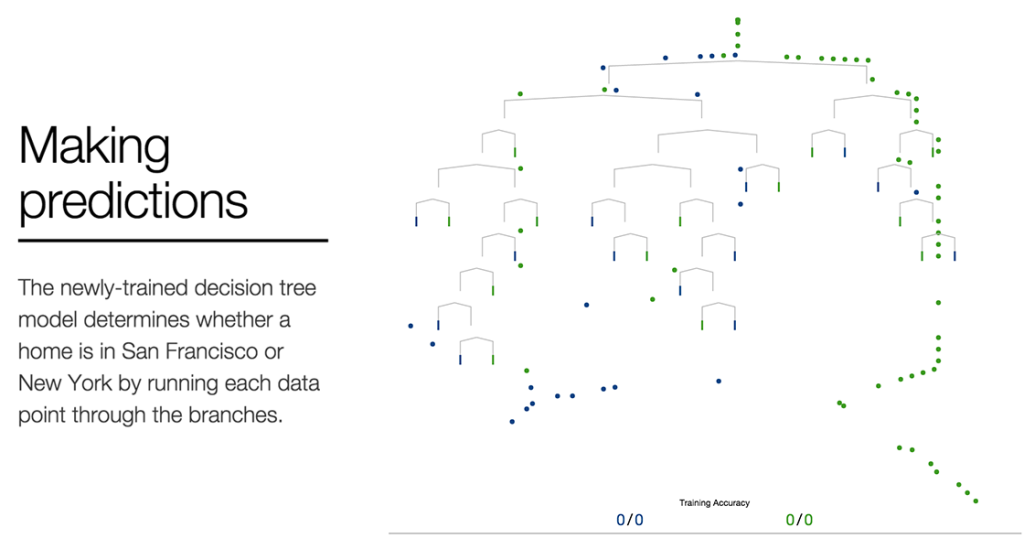
Finding better boundaries Let’s revisit the 240-ft elevation boundary proposed previously to see how we can improve upon our intuition. Clearly, this requires a different perspective. By transforming our visualization into a histogram, we can better see how frequently homes appear at each elevation. While the highest home in New York is ~240 ft, the […]
$96 3D-printed rocket that recalculates its mid-air trajectory using a $5 sensor
30 Second Overview Full System Overview (5 minutes)https://www.youtube.com/watch?v=DDO2EvXyncE&t=54s Full Development Media and Documentationhttps://drive.google.com/drive/folders/17zpks6_R59H0iXJaGkTrtp1SzIFFAQtY?usp=sharing The Google Drive archive contains additional development media and documentation including: mechanical design and assembly system electronics and firmware testing launch tests and rocket motor development system flow diagram rocket specifications bill of materials and cost breakdown Project Overview This project is […]
LotusNotes
2026-03-14 I tend to focus on the origin of the computer within the military. Particularly in the early days of digital computing, the military was a key customer, and fundamental concepts of modern computing arose in universities and laboratories serving military contracts. Of course, the war would not last forever, and computing had applications in […]
The Appalling Stupidity of Spotify’s AI DJ
February 26, 2026New York, NY Am I naïve in expecting Artificial Intelligence to be smart? Is my interpretation of the word “intelligence” too literal? And when an AI behaves stupidly, who’s to blame? The programmers or the AI entity itself? Is it even proper to make a distinction between the two? Or does the AI […]
SpiceCrypt: A Python library for decrypting LTspice encrypted model files
A specialized Python library for decrypting LTspice® encrypted model files. It supports both the text-based format (.CIR / .SUB files using a modified DES variant) and the Binary File format (a two-layer XOR stream cipher), with automatic format detection. Installation Install as a tool with uv: uv tool install git+https://github.com/jtsylve/spice-crypt.git Or add as a dependency […]
Leviathan
Leviathan | Project Gutenberg *** START OF THE PROJECT GUTENBERG EBOOK 3207 *** By Thomas Hobbes 1651 LEVIATHAN OR THE MATTER,FORME, & POWER OF A COMMON-WEALTHECCLESIASTICAL AND CIVILL Thomas Hobbes of Malmesbury Printed for Andrew Crooke, at the Green Dragon in St. Paul’s Churchyard,1651. TRANSCRIBER’S NOTES ON THE E-TEXT: This E-text was prepared from the […]
Rack-Mount Hydroponics

rack-mount hydroponics early 2026 i started growing lettuce in a spare server cabinet. this is, for many reasons, a terrible idea. here’s how i did it. backstory for reasons i won’t explain here (because i genuinely can’t) we ended up with two whole 42u rack cabinets when we only really needed about 10u. also, it […]
A most elegant TCP hole punching algorithm
TCP hole punching is a way to connect two computers behind NAT routers. The technique has a lot of requirements to work. Both sides must know each other’s WAN IPs They must know the right external ports to use They must connect at exactly the same time In practice this collapses to using STUN to […]
Federal Surveillance Tech Becomes Mandatory in New Cars by 2027

Your next car purchase comes with an unwelcome passenger: a federal mandate requiring surveillance technology that monitors your every blink, glance, and head nod. Thanks to Section 24220 of the 2021 Infrastructure Investment and Jobs Act, NHTSA must finalize rules forcing all new passenger vehicles to include “advanced impaired driving prevention technology”—essentially turning your dashboard […]
Tree Search Distillation for Language Models Using PPO
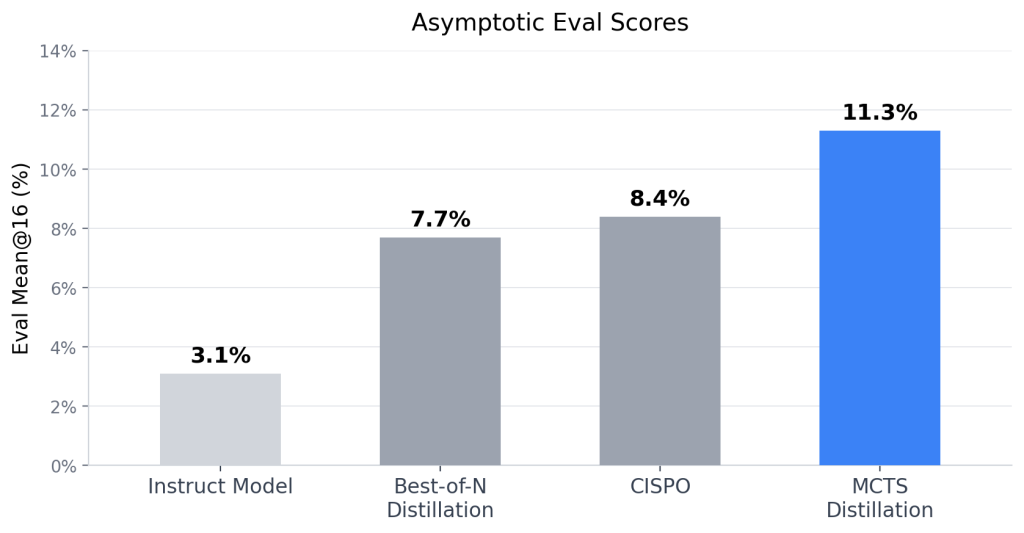
03-01-2026 · Updated 03-03-2026 Game-playing neural networks like AlphaZero achieve superhuman performance in board games by augmenting the raw policy with a test-time search harness and distilling the stronger, augmented policy back into the network. Why aren’t similar techniques used in language modelling today? The DeepSeek-R1 authors mention they found limited success with MCTS; Finbarr […]