The RCE that AMD wouldn’t fix
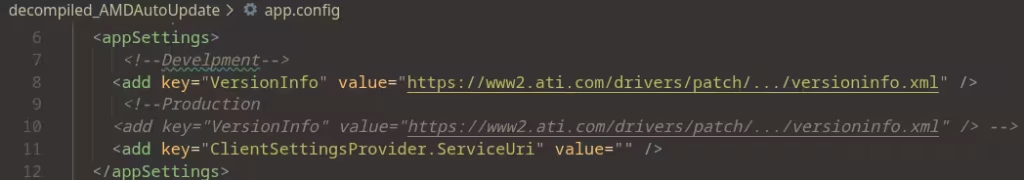
After being interrupted multiple times by an annoying console window that would pop up periodically on my new gaming PC, I managed to track the offending executable down to AMD’s AutoUpdate software. In my frustration, I decided to punish this software by decompiling it to figure out how it worked, and accidentally discovered a trivial […]
FPS.cob: A first person shooter in COBOL
FPS.cob is what you get when you decide that game development is too easy nowadays. Enjoy what can only be described as an out-of-body experience in the ways of COBOL tomfoolery. It supports two level styles: map/level1.map: the original grid-based Wolf3D-style path. map/doom_sectors.map: a sector/linedef map with doors, different heights (so DOOM-like). Requirements cobc ffplay […]
Nextcloud Hub 26 Spring: Built together, designed for the future

[embedded content] A decade of privacy, sovereignty and collaboration Ten years ago, we built Nextcloud to solve a problem that is even more pressing today: the dependence on centralized, proprietary software that threatens our privacy and sovereignty. Organizations need a future-proof framework to replace centralized, legacy collaboration tools. One that only open source can provide. […]
Open Reproduction of DeepSeek-R1

A fully open reproduction of DeepSeek-R1. This repo is a work in progress, let’s build it together! Table of Contents Overview Plan of attack Installation Training models Evaluating models Reproducing Deepseek’s evaluation results Data generation Contributing The goal of this repo is to build the missing pieces of the R1 pipeline such that everybody can […]
Lines of Code Got a Better Publicist

It’s fifteen years ago (bear with me, I’ve been in this industry since the late 90s, most of my good stories start this way), and you’ve got two senior developers at a SaaS company. One of them writes 40% more lines of code than the other. Is that developer better? More impactful for the business? […]
HTML is a native image format, hear me out
composability, not pixels The next thing a model generates isn’t an image.It’s a document. An image flattens everything into one frozen raster. HMML keeps the pieces – vector, text, raster, 3D, motion – composable and editable, created at the grain of a node, not a 1024-grid of guesses. 01 Composable, not flattened A photo, an […]
Web Browsers on Video Game Consoles

Video game consoles have a long history with web browsers. From the advent of the World Wide Web, consoles have been trying to get online. Browsers on video game consoles were initially very much an attempt to provide a cheap gateway to the web for a casual audience lacking technical expertise, though as time progressed […]
Why AI hasn’t replaced software engineers, and won’t
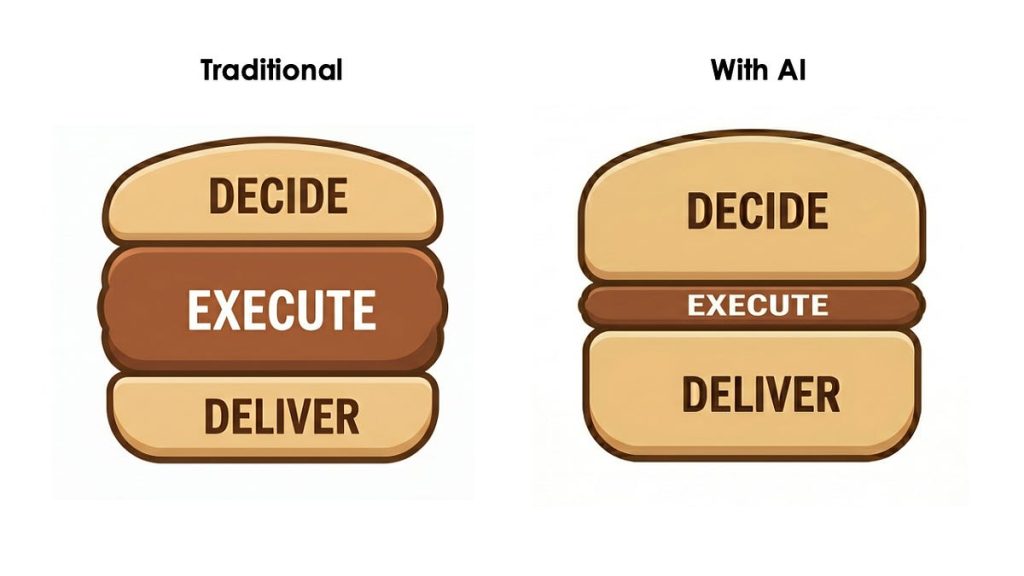
There is great anxiety and uncertainty about AI replacing jobs. How can we move past vague warnings and bombastic predictions and bring data to bear on this question? One good way is to look at the profession where AI capabilities are furthest along and adoption has been exceptionally rapid: software engineering. In this essay, we […]
Macaroni – a single HTML file messenger
A messenger implemented as a single HTML file Russian version: README.ru.md. License: DO WHAT THE FUCK YOU WANT TO PUBLIC LICENSE. The demo opens a hardcoded read-only .macaroni dataset, so the first screen does not burn unauthenticated GitHub API rate limit. No token. No registration. No backend. You can read demo .macaroni chats immediately. To […]
AI agent runs amok in Fedora and elsewhere

Agentic AI systems can be used to do a variety of things autonomously on behalf of a human user: open or manage bugs, generate code, submit pull-requests, and (apparently) even complain about rejection. In May, a Fedora developer discovered that an allegedly rogue agent had been pestering the project in a number of ways: reassigning […]