Tailscale’s New macOS Home
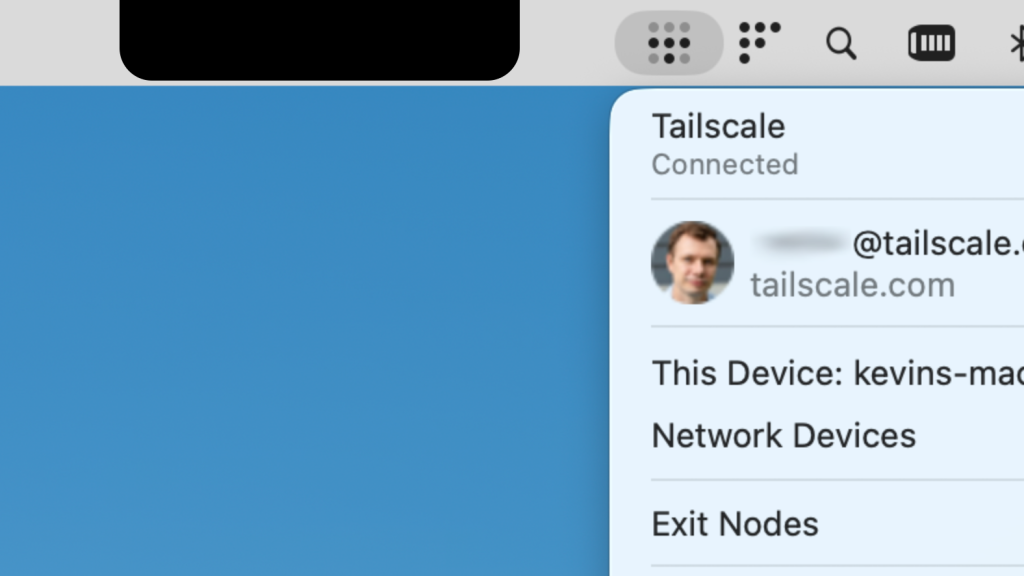
Tailscale should feel nearly invisible when it’s connecting you and all your devices together. But on some MacBooks, for a while there, it could be a little too invisible. We have two fixes for it: one small and slightly quirky, and another really useful one, available now on macOS. The small, quirky fix might become […]
Hugo’s New CSS Powers

As I mentioned in my previous post, I was intrigued when the release of Hugo v.0.158.0 introduced its css.Build function. The new powers that resulted are worth a look when you consider all the aspects of styling a site you’ve built, or plan to build, on Hugo. Still, the enhancements have certain limitations of which […]
Cursor 3
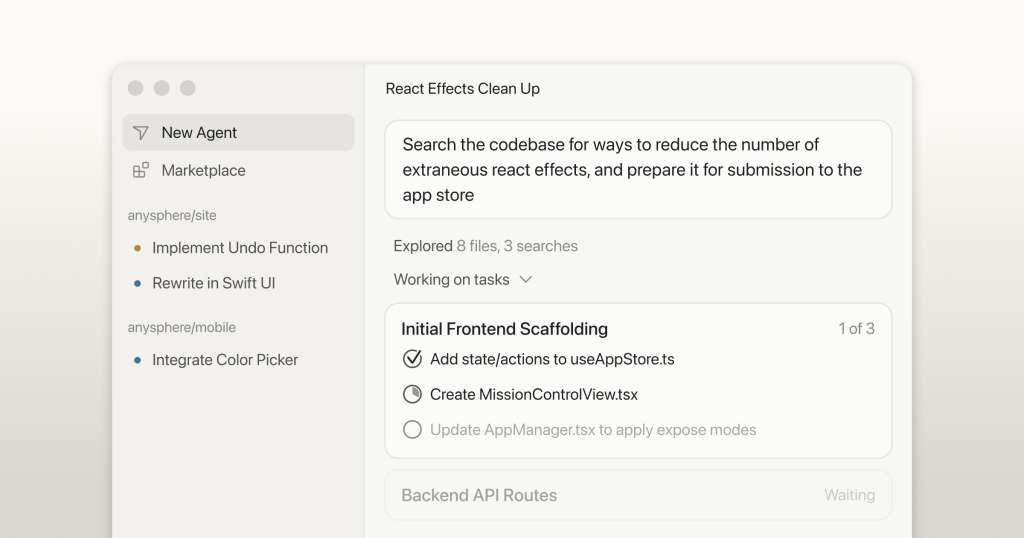
Software development is changing, and so is Cursor. In the last year, we moved from manually editing files to working with agents that write most of our code. How we create software will continue to evolve as we enter the third era of software development, where fleets of agents work autonomously to ship improvements. We’re […]
Good ideas do not need lots of lies in order to gain public acceptance (2008)
A subtle change has been made to the comments links, so they no longer pop up. Does this in any way help with the problem about comments not appearing on permalinked posts, readers? Update, September 2008. Hullo there Paul Krugman readers. Yes, I did say ”Good ideas do not need lots of lies told about […]
A $1.75T IPO Would Be Overpaying 30% for SpaceX
SpaceX filed confidentially for an IPO on April 1, 2026, targeting a $1.75 trillion valuation and a June listing. If completed, it would be the largest IPO in history. I found this valuation interesting because SpaceX is a conglomerate now, so valuing the business segments together has a lot of intangible value. But my particular […]
Google releases Gemma 4 open models

Gemma 4 models undergo the same rigorous infrastructure security protocols as our proprietary models. By choosing Gemma 4, enterprises and sovereign organizations gain a trusted, transparent foundation that delivers state-of-the-art capabilities while meeting the highest standards for security and reliability.
Decisions that eroded trust in Azure – by a former Azure Core engineer
Inside the complacency and decisions that eroded trust in Azure—from a former Azure Core engineer. This is the first of a series of articles in which you will learn about what may be one of the silliest, most preventable, and most costly mishaps of the 21st century, where Microsoft all but lost OpenAI, its largest […]
Artemis II will use laser beams to live-stream 4K moon footage at 260 Mbps
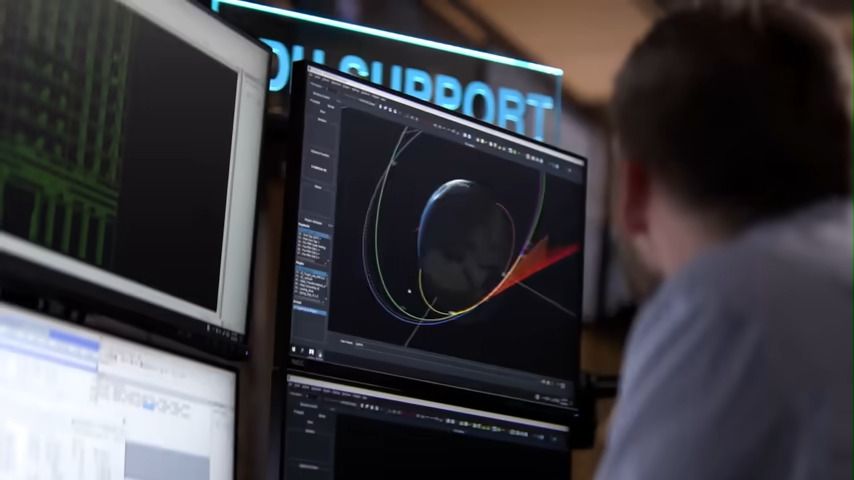
NASA’s Artemis II mission blasted off on Wednesday. Now brace yourselves for exciting high-resolution 4K footage live-streamed from the surface of the moon thanks to NASA’s laser-based O2O system. The cutting-edge Orion Artemis II Optical Communications system (O2O) will be used to beam 4K moon footage at up to 260 Mbps. We should also be […]
Delve allegedly forked an open-source tool and sold it as its own

The controversy surrounding compliance startup Delve has gone from bad to worse this week. Among the fresh allegations from the anonymous whistleblower known as DeepDelver is the claim that Delve allegedly took an open source tool and passed it off as its own work without proper license attribution to or monetary agreement with the original […]
LinkedIn Is Illegally Searching Your Computer
Microsoft is running one of the largest corporate espionage operations in modern history. Every time any of LinkedIn’s one billion users visits linkedin.com, hidden code searches their computer for installed software, collects the results, and transmits them to LinkedIn’s servers and to third-party companies including an American-Israeli cybersecurity firm. The user is never asked. Never […]