Fix Your Tools

Last week I had to diagnose a bug in an open source library I maintain. The issue was gnarly enough that I couldn’t find it right away, but then I thought: if I set a breakpoint here and fire up the debugger, I will likely find the root cause very soon… and then proceed to […]
Extending C with Prolog (1994)
Extending C with Prolog (This is an expanded version the text of an article which appeared in the August 1994 issue of Dr. Dobbs Journal. Please do not copy or distribute without acknowleging Dr. Dobbs Journal. The original article referred to Cogent Prolog, which has been renamed Amzi! Prolog. As the article was intended for […]
We hid backdoors in ~40MB binaries and asked AI + Ghidra to find them
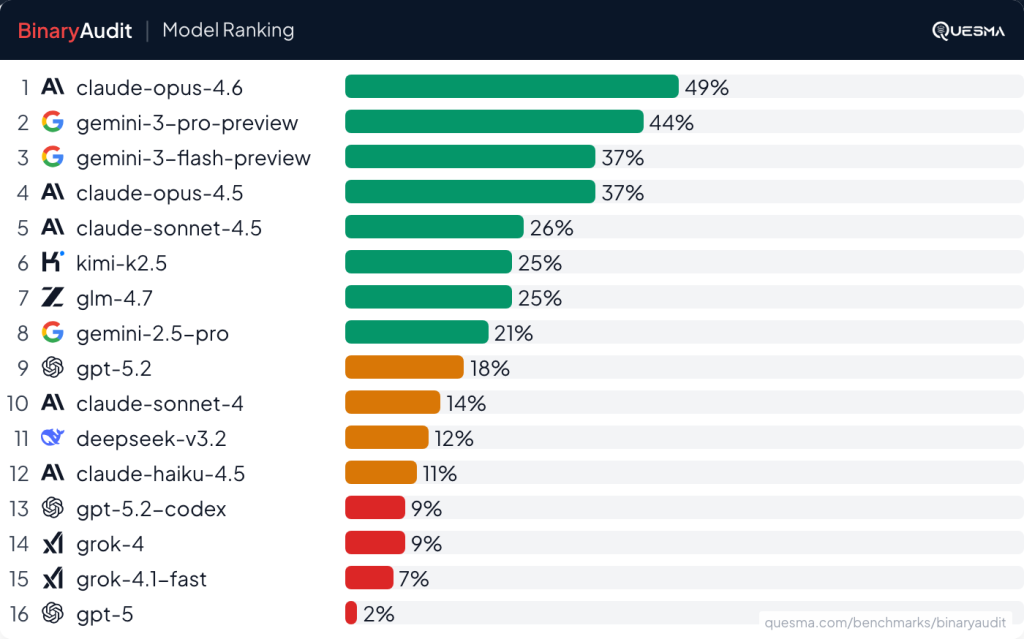
Claude can code, but can it check binary executables? We already did our experiments with using NSA software to hack a classic Atari game. This time we want to focus on a much more practical task — using AI agents for malware detection. We partnered with Michał “Redford” Kowalczyk, reverse engineering expert from Dragon Sector, […]
Man accidentally gains control of 7k robot vacuums
Get the Popular Science daily newsletter💡 Breakthroughs, discoveries, and DIY tips sent six days a week. A software engineer’s earnest effort to steer his new DJI robot vacuum with a video game controller inadvertently granted him a sneak peak into thousands of people’s homes. While building his own remote-control app, Sammy Azdoufal reportedly used an […]
Git’s Magic Files

A follow-up to my post on extending git functionality. Git looks for several special files in your repository that control its behavior. These aren’t configuration files in .git/, they’re committed files that travel with your code and affect how git treats your files. If you’re building a tool that works with git repositories, like git-pkgs, […]
Scipy.stats. Chatterjeexi
Generate perfectly correlated data, and observe that the xi correlation is nearly 1.0. >>> import numpy as np >>> from scipy import stats >>> rng = np.random.default_rng() >>> x = rng.uniform(0, 10, size=100) >>> y = np.sin(x) >>> res = stats.chatterjeexi(x, y) >>> res.statistic np.float64(0.9012901290129013) The probability of observing such a high value of the […]
Volatility: The volatile memory forensic extraction framework
Volatility is the world’s most widely used framework for extracting digital artifacts from volatile memory (RAM) samples. The extraction techniques are performed completely independent of the system being investigated but offer visibility into the runtime state of the system. The framework is intended to introduce people to the techniques and complexities associated with extracting digital […]
Attention Media ≠ Social Networks
By Susam Pal on 20 Jan 2026 When web-based social networks started flourishing nearly two decades ago, they were genuinely social networks. You would sign up for a popular service, follow people you knew or liked and read updates from them. When you posted something, your followers would receive your updates as well. Notifications were […]
Minions: Stripe’s one-shot, end-to-end coding agents – Stripe Dot Dev Blog
Alistair Gray Alistair is a software engineer on the Leverage team. The Leverage team builds surprisingly delightful internal products that Stripes can leverage to supercharge their productivity. Minions: Stripe’s one-shot, end-to-end coding agents—Part 2
What Is a Database Transaction?
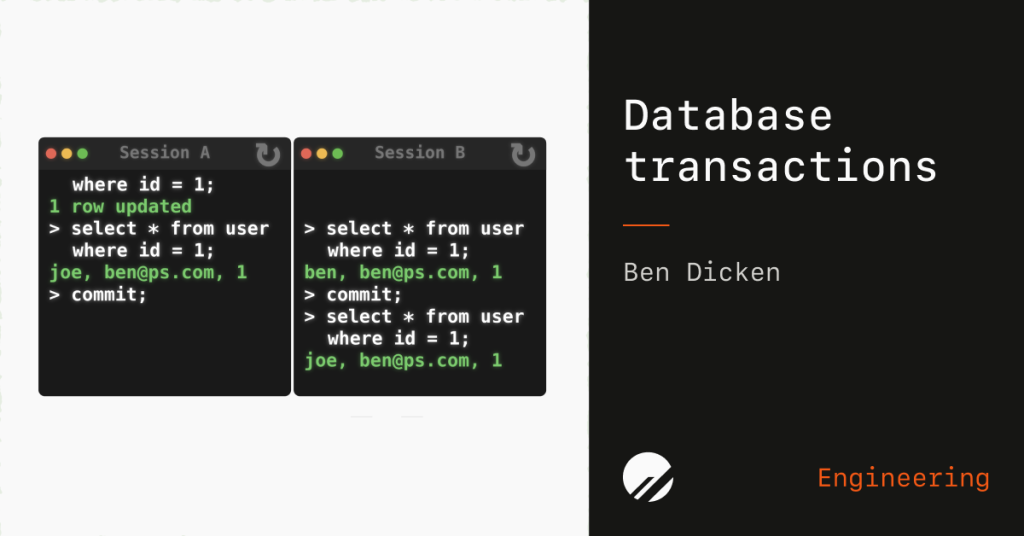
By Ben Dicken | January 14, 2026 Transactions are fundamental to how SQL databases work. Trillions of transactions execute every single day, across the thousands of applications that rely on SQL databases. A transaction is a sequence of actions that we want to perform on a database as a single, atomic operation. An individual transaction […]