Timeline: Anthropic, OpenAI, and U.S. Government
Feb 28, 2026, 02:56 AM OpenAI agrees with Dept. of War to deploy models in classified network OpenAI strikes deal with Pentagon to supply AI to classified military networks. Altman says the same red lines at the heart of Anthropic’s dispute are enshrined in OpenAI’s new partnership: ”Two of our most important safety principles are […]
What AI coding costs you
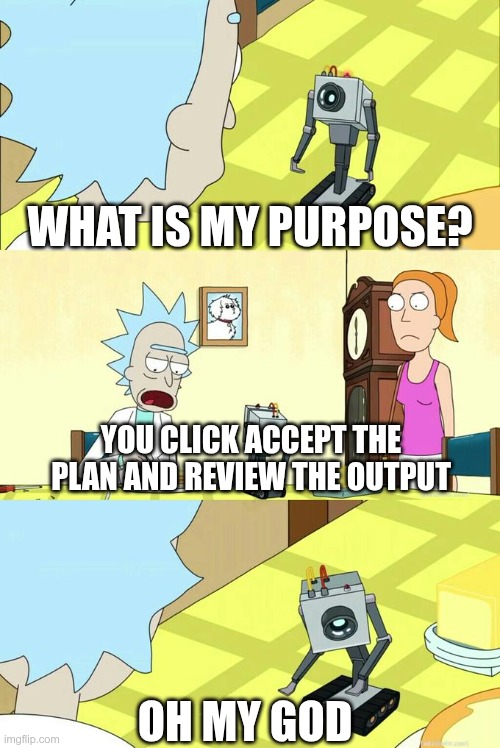
Every developer I know uses AI for coding now. The productivity gains are real, but there are costs that don’t show up on any dashboard. Imagine a spectrum. On the far left are humans typing on the keyboard, seeing the code in the IDE. On the far right: AGI. It implements everything on its own. […]
Don’t trust AI agents

When you’re building with AI agents, they should be treated as untrusted and potentially malicious. Whether you’re worried about prompt injection, a model trying to escape its sandbox, or something nobody’s thought of yet, regardless of what your threat model is, you shouldn’t be trusting the agent. The right approach isn’t better permission checks or […]
Show HN: SplatHash – A lightweight alternative to BlurHash and ThumbHash
SplatHash encodes any image into exactly 16 bytes (a 22-char base64url string) and decodes it back to a 32×32 blurry preview in 0.067 ms. Go, TypeScript, and Python all produce bit-for-bit identical hashes. Columns: original · SplatHash 32×32 · ThumbHash · BlurHash. Regenerate: mise run compare. Go is the reference implementation. All others are verified […]
Unsloth Dynamic 2.0 GGUFs
copyCopychevron-down Basics A big new upgrade to our Dynamic Quants! We’re excited to introduce our Dynamic v2.0 quantization method – a major upgrade to our previous quants. This new method outperforms leading quantization methods and sets new benchmarks for 5-shot MMLU and KL Divergence. This means you can now run + fine-tune quantized LLMs while […]
US and Israel carrying out strikes against Iran

US President Donald Trump had been sending mixed signals about whether he planned to attack Iran, preparing for war while saying he favors dialogue. The United States has moved military assets closer to the Middle East over the past few weeks, raising concerns that the prospects of war were growing. Trump said on January 22 […]
Israel launches strike against Iran, declares state of emergency across country

The United States and Israel launched attacks on Iran Saturday – marking a major escalation following weeks of negotiations between US and Iranian officials over the country’s nuclear program. President Donald Trump confirmed in a video posted to social media that the United States had begun a “massive and ongoing” military campaign in Iran, “to […]
Rust Is Just a Tool
Rust is Just a Tool Blog Talks Contact 4 Feb 2026 I like Rust. It’s versatile enough that it can be used for application and systems programming. It has the best tooling of any language I’ve seen. It has a fairly pleasant type system. And I think most importantly it does a great job in […]
Cash issuing terminals
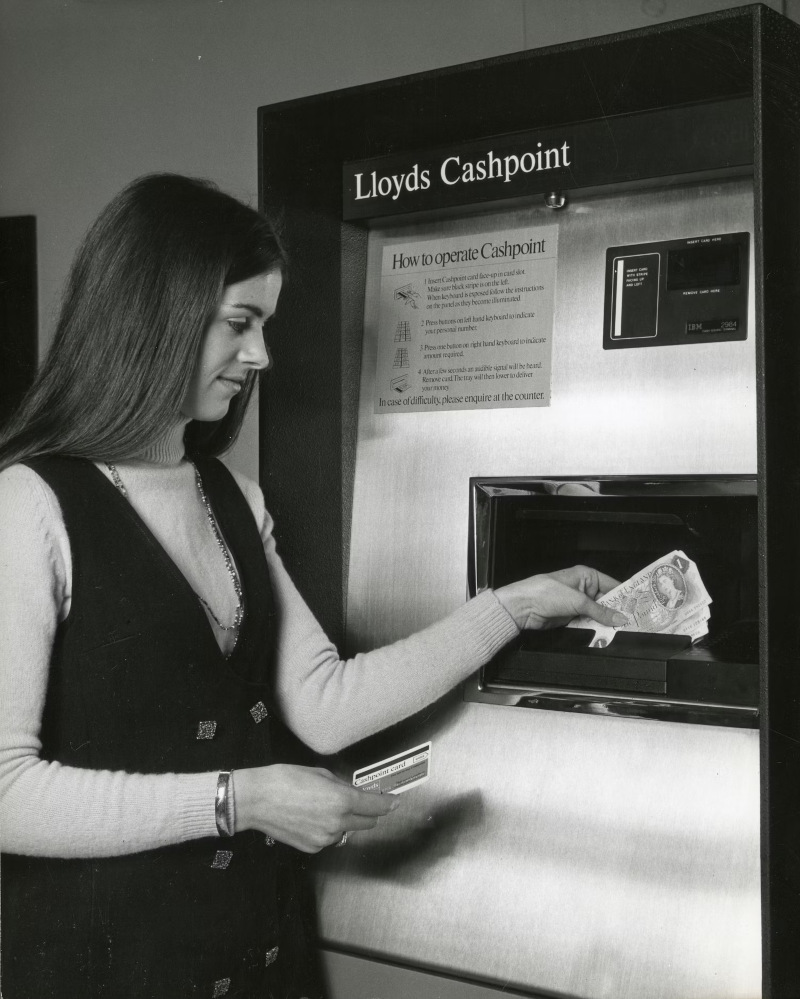
2026-02-27 In the United States, we are losing our fondness for cash. As in many other countries, cards and other types of electronic payments now dominate everyday commerce. To some, this is a loss. Cash represented a certain freedom from intermediation, a comforting simplicity, that you just don’t get from Visa. It’s funny to consider, […]
Don’t use passkeys for encrypting user data
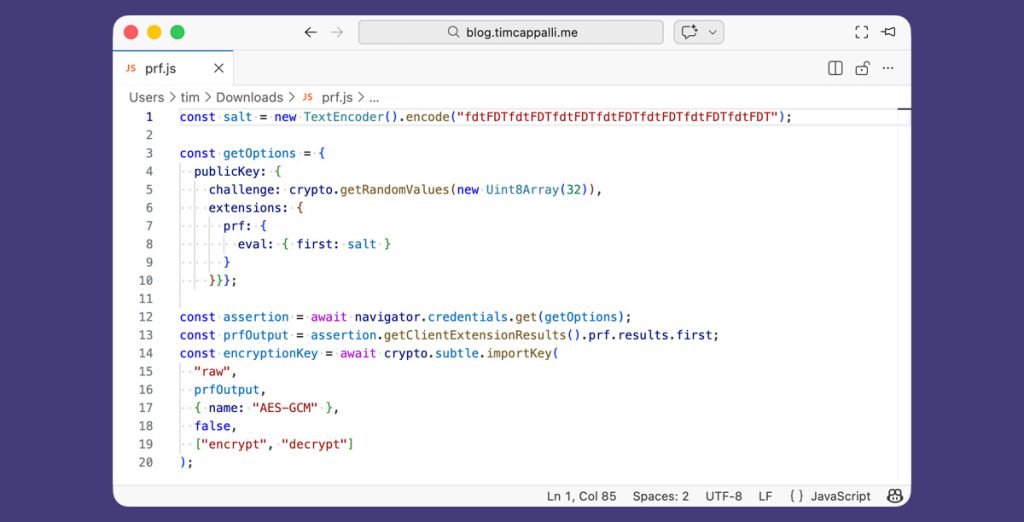
Why am I writing this today? Because I am deeply concerned about users losing their most sacred data. Over the past year or two, I’ve seen many organizations, large and small, implement passkeys (which is great, thank you!) and use the PRF (Pseudo-Random Function) extension to derive keys to protect user data, typically to support […]